Introduction
to product security vulnerabilities
Nordic Semiconductor ASA is committed to resolving vulnerabilities to meet the needs of its customers and the broader technology community. This document describes Nordic Semiconductor’s policy for receiving reports related to potential security vulnerabilities in its products and services.
Nordic Semiconductors Product Security Incident Response Team (PSIRT) responds to reported security vulnerabilities in Nordic Semiconductors Products (Hardware and Software), Documentation and Services. The PSIRT ensures that security vulnerabilities are analyzed, documented and communicated in a responsible manner.
Reporting
product security vulnerabilities
If you have discovered a potential security vulnerability in a Nordic Semiconductor product or service, please submit a vulnerability report through this form.
Responsible Disclosure
The ability to upgrade/patch/fix Nordic Semiconductors products in the field varies between our products and can sometime only be done by upgrading the functionality in our silicon in the next version of the chips.
Nordic Semiconductor intends to notify the affected customers, when appropriate, about the vulnerability either through targeted communication to affected customers or through public communication (e.g in a security advisory or a bulletin)
Vulnerability handling process
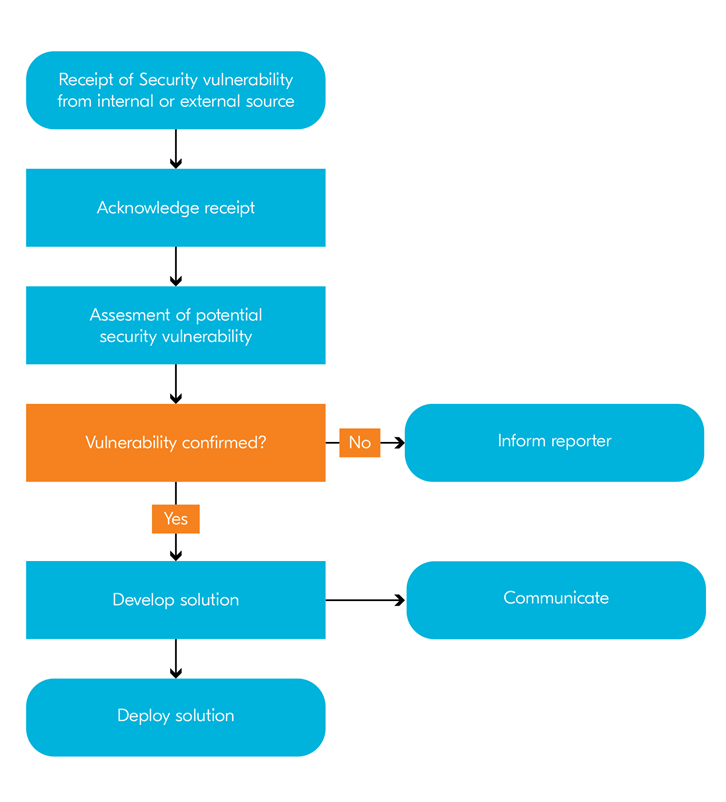
The PSIRT handles reported security vulnerability through the following process:
YesWeHack
Bug bounty program
Nordic Semiconductor sponsors a bug bounty program on YesWeHack, a security platform powered by ethical hackers. They stress test our hardware and software to find any potential or latent security vulnerabilities so they can be fixed before a cybercriminal finds them. The program will cover all of Nordic’s latest silicon product series, engineering samples, dev kits, software and reference designs.

For now, the Nordic Semiconductor YesWeHack bug-bounty program will be run privately (invitation only) as Nordic wants to focus on building up a relationship with the community, while prioritizing report quality and report response times. Any interested hacker is invited to make contact via the YesWeHack platform support team.